What do HIPAA, HITECH, FACTA, GLBA, FERPA, ECPA, COPPA, VPPA, CCPA, CPRA, BIPA, CDPA, CPA, CPDPOM, MOCA, MDPL, and NYPA all have in common?
They’re all acronyms for regulations requiring organizations to protect personal information. Some of them are national regulations aimed at specific types of personal information, such as personal medical or financial data. Others are state regulations that apply to protecting all forms of personal information.
And the list is growing fast.
At the federal level, the proposed ADPPA (American Data Privacy and Protection Act) has already passed the House Energy and Commerce Committee, while at the same time, more than a dozen states have similar new regulations somewhere in their legislative process.
How can any organization expect to keep pace?
Don’t despair. There are two principles that can save your company from the most devastating consequences of non-compliance.
The first principle is knowing (and acting like) your organization is already required to comply. It might seem obvious to some, but the stakes are high and there are still many organizations that are acting like there’s nothing to worry about. As it is often said, you can’t fix something until you admit that a problem exists. If your organization has employees or customers, it is covered by at least one data protection regulation and the biggest risk of all is ignoring that fact.
The second principle, and where you can take some refuge, is that regulators only expect your organization to do what is reasonable. It is called the “Reasonableness Principle,” and it is used as a litmus test for determining compliance.
Basically, it asks the question, would a rational person determine the action to comply was reasonable. For instance, would a rational person believe it is reasonable to put personal information in the wastebasket? Would a rational person believe it is reasonable not to train employees that personal information must be protected? Would a rational person believe an organization could be compliant with a regulation if no one within the organization is accountable?
When the U.S. Department of Health and Human Services (HHS) was asked what type of HIPAA violation would be considered willfully negligent, the example they gave was finding health information in the trash and discovering after that the hospital had not trained their employees about data destruction. In this example, willful negligence is not that the personal information had been placed in the trash. It was learning that the hospital had never trained the employee on the importance of proper destruction. Had the employee been trained, then acted contrary to that training, the fault would not lie with the hospital. The hospital, as HHS explained it, would have done all they could reasonably do and so would be held harmless.
The Big Question
If there is one weakness in the reasonableness fail-safe to compliance, it is knowing what criteria to evaluate, or, in other words, what questions to ask. Fortunately, there are two ways to approach this challenge.
The first approach is to start with the question, how are we protecting personal information now and would our clients and employees agree that it is reasonable?
This approach, of course, requires an assessment of all the ways in which personal information is collected, transmitted, stored, and destroyed. In regulatory parlance, this is known as a Data Protection Impact Assessment (DPIA). Then, with the DPIA in hand, the reasonableness of the processes can be questioned.
The second approach is to hire it out. There is no shortage of data security professionals who specialize in providing DPIAs and recommending reasonable ways of mitigating the risks.
Shred Vault Can Help Too
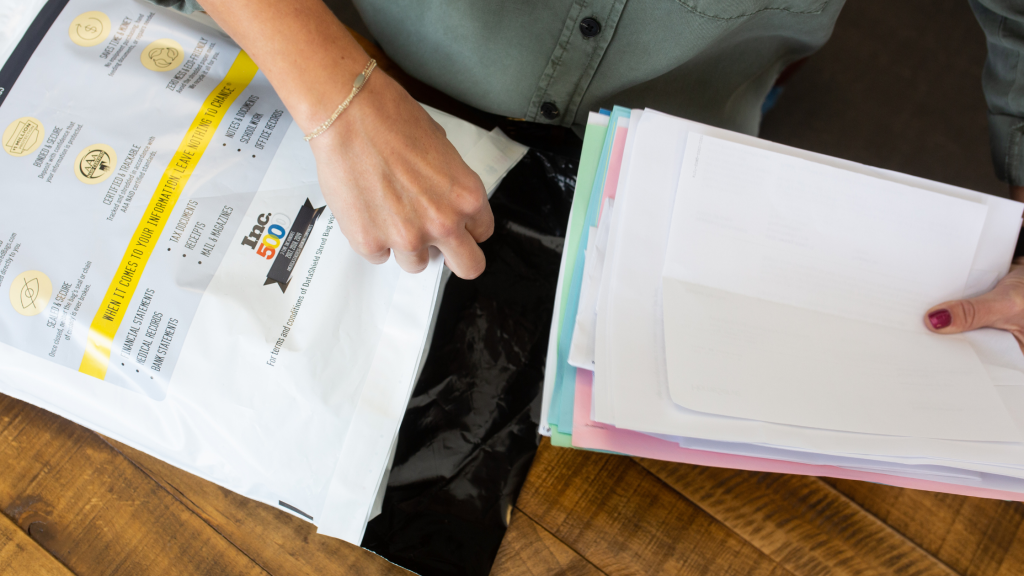
The final disposal of records and electronic equipment represents one of information protection’s most critical processes. It was no accident that HHS referenced information disposal in the example above. They, like every other regulator, understand that improper disposal of personal information is where many organizations drop the ball. They are also highly sensitive to the fact that bad guys are very aware of this vulnerability and can easily exploit it.
Contact us today to learn more about our solutions for routine shredding, electronic media destruction, large clean outs, and Shred Vault deposit locations.
After all, using Shred Vault is the reasonable thing to do.
© 2023 Shred Vault, LLC – All rights reserved